FACIAL RECOGNITION | 6 MIN READ
Facial recognition is a buzzword that's been the topic of many news articles and the subject of various movies. While some see this technology as dystopian, others see it as a futuristic way to further streamline our everyday lives. Keep reading for a crash course on facial recognition technology.
Not enough time? Jump to:
Integration Opportunities for Businesses
Can Facial Recognition Be Fooled?
How Does It Work?
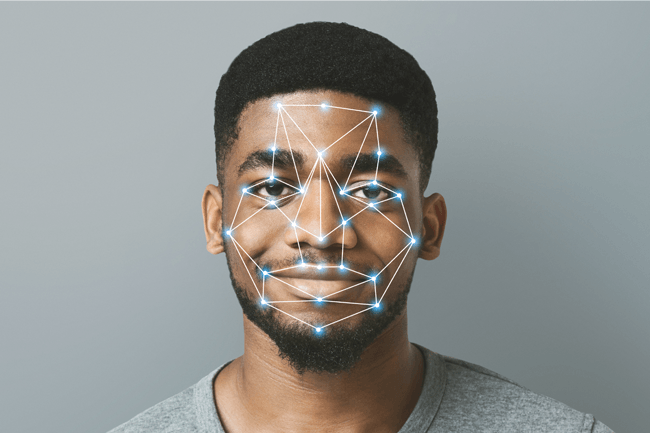
Facial recognition technology uses biometrics to map a user's facial features from a photograph or video. Biometrics are biological measurements such as one's eyes or face shape that can be used to uniquely identify an individual.
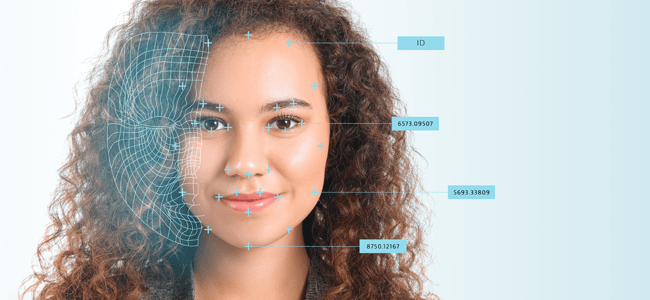
To build this map, also known as a facial signature, facial recognition technology notes a number of unique characteristics on one's face, with key factors including the distance between one's eyes and the distance from one's forehead to their chin.
A facial signature comprised of a complex mathematical formula is then created using this data. After mapping an individual's face, this technology then compares this information with a database of known faces to find a match. Some databases can contain hundreds of millions of photos or more.
To improve a facial recognition system's accuracy, developers tend to rely on machine learning, a sub-field of artificial intelligence. Machine learning involves computers teaching themselves tasks to independently improve their skills sets.
When it comes to improving the accuracy of a facial recognition system, machine learning is used to reward the computer for correct facial identifications and penalizing it for mis-identifications.
In this environment, over time, the system learns to distinguish human faces from other objects, and then how to accurately distinguish one face from another. To distinguish one face from another, the system uses a complex variety of anatomical features previously described, such as one's eyes or the distance between one's eyes.
Privacy Concerns
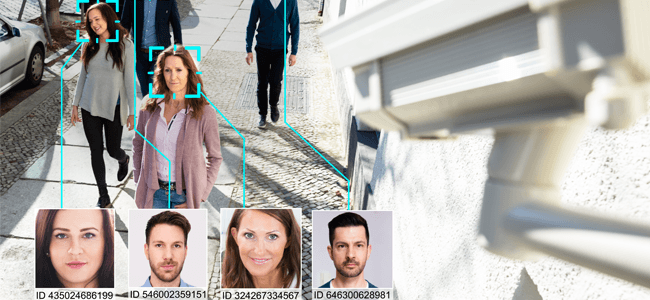
The growing adoption of this technology into everyday life has raised privacy concerns from citizens and corporations alike. People want to know where the pictures stored in facial recognition databases are pulled from and who has access to this data.
Some question if the databases are formed from data handed over from social media platforms like Facebook, while others question the usage of traffic light cameras in building these databases.
Citizens especially question the use of facial recognition technology to identify and arrest suspected criminals. Since this technology isn't 100% accurate, this raises concerns about citizens being wrongfully arrested for crimes they didn't commit.
And these concerns are valid, seeing that wrongful arrests due to facial recognition technology are already happening.
Privacy concerns surrounding this technology have begun migrating to the courtroom. Take the Patel v. Facebook court case as proof of how much traction the privacy movement is gaining.
While the Biometric Information Privacy Act, implemented in 2008 to address concerns over biometric data privacy, sets a precedent for Patel v. Facebook, this case is historic because it marks one of the first times that a major company has been taken to court over facial recognition concerns.
Now, there are a host of companies seeking to build the world's largest facial recognition database. Take Clearview as a recent example.
The company found themselves in hot water earlier this year after media outlets began reporting on how Clearview was sourcing billions of pictures from various social media platforms to build a database that law enforcement could then use to identify suspects.
All Hope is Not Lost
To many, facial recognition and privacy don't exactly go hand in hand. Public outcry is beginning to ramp up as more companies are thrust into the spotlight for supposed violations of citizens' privacy.
However, when it comes to the storage and use of your data, the main culprits tend to be major corporations like Facebook and law enforcement agencies. When it comes to local businesses implementing facial recognition technology, the chances that your data has been stored and sold without your knowledge are smaller.
When smaller businesses implement this technology, it is usually for security or attendance purposes. Sometimes, data is stored locally on that organization's network, which means that data stays in-house and isn't stored in or sold to larger companies.
Additionally, sometimes the facial recognition databases are created by those who voluntarily create a user profile. For instance, a local business using facial recognition to clock employees in and out may want them to voluntarily submit a picture of themselves for the database so that it may recognize them when they get scanned.
In this scenario, the database was not created by aggregating pictures from one's social media profiles without their consent. For other facial recognition applications, such as scanners to provide security clearance, those who aren't already registered in the database as an authorized visitor likely will not have their data stored.
For instance, if a facial recognition kiosk was used to grant access to a secure portion of a building, maybe only those who have access will have their profile stored. Other visitors will simply be turned away and their data won't really be stored because they don't have a registered profile.
RELATED: Can Businesses Be Sued for Data Breaches?
Integration Opportunities for Businesses
Facial recognition has many potential integration applications for businesses. Companies researching a job candidate can even use facial recognition technology to find a candidate's personal social media profiles.
The Department of Homeland Security uses this technology in airports and at border crossings to search for those who are overstaying their visas, have fake passports, or are under criminal investigation. Local police have also been using this technology to identify and arrest protesters.
Retail stores can utilize this technology combined with security cameras to identify suspicious individuals and shoplifters.
When it comes to advertising, marketers hope to use facial recognition technology for hyper-personalized re-marketing campaigns.
For instance, if you walk past a billboard for Coke, the billboard could have a camera that identifies you as having seen the ad. Then, over the course of the next few days, Coke could send you personalized Coke ads on social media and other websites.
Corporate offices, factories, and schools alike can use this technology to take attendance and track visitors. For areas with higher security clearance, facial recognition can be used to restrict access.
There is a cutting-edge innovation that can do all of the aforementioned tasks and more. Known as temperature scanning kiosks, these devices are being integrated by many businesses.
What is a Temperature Scanning Kiosk?
Temperature scanning kiosks use a combination of facial recognition and infra red technology to identify an individual, assess their temperature through their forehead, and store this data for tracking purposes.
These kiosks are best suited for businesses who wish to monitor visitor traffic as well as mitigate the spread of potentially infectious conditions.
To use one of these kiosks, an individual must step within the target range, which is usually about 1-3 feet. Using infra red technology, the kiosk will scan the individual’s forehead and take their temperature.
If an individual has a temperature higher than the allowed threshold, they can be pulled aside for additional screening.
With some brands, user profiles can be created to recognize repeat visitors and historically track their temperatures. This is useful in the event of having to contact trace an individual who becomes sick with a contagious condition.
RELATED: Temperature Scanners for Businesses [Types + Pricing]
Can Facial Recognition Be Fooled?
While facial recognition technology is consistently improving, it still has a ways to go before it's infallible.
There have been instances when someone has been able to fool it by wearing a disguise, holding up a picture on their phone, or, in a particularly complex scenario, wearing a printed lifelike mask resembling someone else's face.
There are two main ways in which people have been able to fool facial recognition systems: through obstruction of one's face or by confusing the system into mis-identifying a face.
Obstruction
By cleverly covering one's face, an individual may be able to trick a facial recognition system into simply thinking that they're a non-human object passing through.
Many try to thwart these systems by simply wearing a mask or hat. However, the main areas that a facial recognition system scans are the eyes, mouth, and nose. By simply wearing a mask or hat, some of these crucial facial points are still exposed, which means that a system can still identify an individual.
Some people go to extreme lengths to ensure that their entire face, including the mouth, nose, and eyes, are covered.
While wearing a covering like this may effectively trick the system, it is also conspicuous, which makes these types of tricksters easy to identify, especially when security personnel are manning facial recognition checkpoints.
Confusion
A more advanced way of fooling a facial recognition system involves the strategic application of makeup, camouflage, or the use of lasers, as seen in the Hong Kong protests.
Strategically applying makeup that either covers the main facial recognition points or strategically deflects light off certain parts of the face can scramble a facial recognition system by making it identify an individual as something else.
However, the flaw in this method is that there are different types of facial recognition software, so to effectively trick a system, a user must know what type of system is utilized in the area they're trying to gain access to.
Special camouflaged material such as scarves and earrings can be worn inconspicuously to confuse a facial recognition system.
Designers have created camouflage with a pattern that a computer will register as a bunch of faces. When a computer scans an individual wearing this camouflage, it may become overwhelmed by the sheer number of faces, which can allow said individual to exploit the system.
By pointing handheld lasers at the camera on a facial recognition system, one can disable the sensors in the camera, effectively stopping the system from scanning.
RELATED: Social Engineering Trends in 2020
How to Stop Tricksters in Their Tracks
Businesses can minimize the odds that a user fools facial recognition by requiring visitors to not wear material that shields their face, at the very least when passing through facial recognition checkpoints.
Having security personnel at checkpoints can also ensure that suspicious individuals trying to trick the system are quickly identified. Facial recognition tricksters can also be thwarted by requiring multiple verifications at a checkpoint.
For instance, at an airport, if one's face has to be scanned before boarding a plane, maybe they also have to provide a form of identification such as a driver's license, or a date of birth.
While facial recognition technology raises some privacy concerns that will likely be addressed in court cases in the coming years, it also has the potential to change life as we know it.
The endless potential applications for this technology means that in the future, we could see facial recognition become as commonplace as social media is now.
To learn more about technology, cyber security, and more, follow our blog!
Posted by Erica Kastner

Erica Kastner is a lead Marketing Specialist at Standard Office Systems as well as a University of Georgia graduate. She aims to use her passion for problem-solving to help businesses understand how to better leverage their network infrastructure.

