CYBER SECURITY | 5 MIN READ
While email filtering has been around in one form or another for a while, it serves a more important role in your cyber security plan than you may think. Keep reading to learn what exactly email filtering is, how it works, and some additional ways in which you can protect your network.
Not enough time? Jump to:
How Does Email Filtering Work?
How Else Can I Protect My Network?
What Is Email Filtering?
When you enable email filtering, you allow the software to independently analyze incoming emails for red flags that signal spam/phishing content and automatically move those emails to a separate folder.
Most major email providers have spam filters built in that move questionable emails to a "Junk" or "Spam" folder. Sometimes, these folders have a setting enabled that automatically deletes all emails in this folder after a specified period.
Spam emails are usually more of an annoyance because they're trying to sell you a product or persuade you into taking some type of action like donating to a cause.
On the other hand, phishing emails pose more of a danger to the security of your personal information. Phishing emails seek to steal your personal information for malevolent means.
Once personal information such as account logins or credit card information is taken, your personal accounts can be hacked or you can become a victim of financial fraud.
There are platforms whose services can be used to monitor for and flag phishing emails. These filters add an extra layer to your email security than just having spam filters enabled.
This software also typically comes with more general web filters that can be used to prevent you from visiting websites known to contain malware.
If you're a business, web filters can be used to boost employee productivity and better protect your network. Web filters can be used to block or warn employees attempting to visit malware-laden websites, or restrict traffic to websites that are common workday distractions, such as social media platforms.
How Does Email Filtering Work?
As described above, email filtering works by analyzing incoming emails for red flags that signal spam or phishing content and then automatically moving those emails to a separate folder.
Spam filters use multiple criteria to assess an incoming email. They look for common trigger words that signal an unwanted email attempting to sell you something, such as "free" and "earn money".
If the sender sends you an email using your email address instead of your contact name, that could trigger your spam filter, seeing as the sender won't be in your contacts. Senders trying to send you content such as newsletters that you haven't opted into may be flagged as spam.
Additionally, if the sender's IP address has previously been flagged for sending spam, a sender with the same IP address will likely be flagged as well.
Even the content and design of the email itself can trigger a spam filter. Gaudy large fonts or large images are two main layout triggers for spam.
If you enable a software that monitors for phishing emails, the criteria is a little different. While all of the above criteria may automatically put an email on a content filter's radar, additional red flags will trigger a phishing filter.
Phishing emails usually include a link or attached document that's filled with malware used to hack your network. Senders who have been flagged for having a history of sending malware may set off a phishing filter.
Emails from unknown senders containing links or attached documents may also set off phishing filters.
Phishing filters will typically move flagged emails to an additional inbox, sometimes labeled as "Other". In this inbox, flagged emails will be put "on hold" until you release, block, or allow it.
If you release an email, then it is sent to your normal inbox to be opened, but in the future you will have to continue approving emails from the sender. If an email is blocked, then the email is rejected and the sender will be now be blocked from sending you future emails.
If an email is permitted, it is delivered to your normal inbox and the sender will automatically be approved to send emails directly to your inbox moving forward.
How Else Can I Protect My Network?

Recognize the Signs of a Scam
While enabling email filtering can prevent phishing and scam emails from victimizing you, sometimes, a few sophisticated ones can make their way through.
Email filters are not enough to protect you from being victimized by a scam. You must learn how to recognize the signs of an email scam if you wish to prevent yourself from falling for one.
There are a few common signs that an email may be a scam or phishing attempt. The first step is knowing the difference between a phishing email and a spam email.
A spam email is relatively harmless. While the email may come from an unknown address or look generally abnormal, these types of emails usually are trying to sell you on something. For instance, a spam email could aim to entice you into buying adult content or reading an unwanted newsletter.
On the other hand, a phishing email is designed to trick you into providing personal information that can be used to hack your private accounts and steal money. There are a few red flags that can be used to quickly recognize and stop a phishing scheme in its tracks:
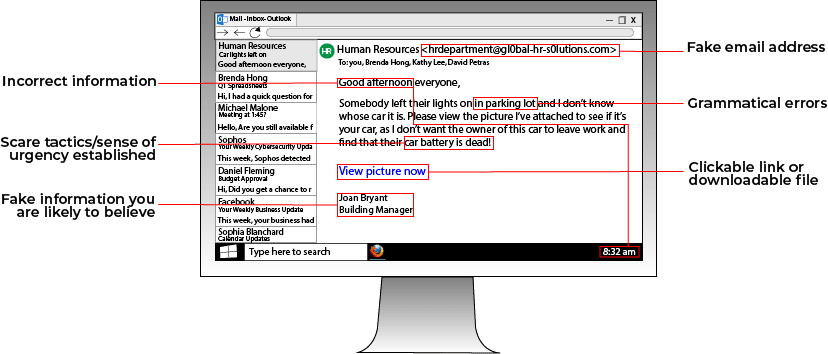
While an email with some of these characteristics won't always be a phishing email, you should automatically be on alert when you notice any of the above signs.
If you're a business, all it takes is one employee falling for a phishing attempt to compromise your entire network. Businesses should hold educational seminars to teach employees about cyber security best practices.
At these seminars, which can take place in person or online, businesses can teach employees about ways to recognize and avoid phishing schemes, create strong passwords, and avoid common cyber threats online.
There are even companies that can conduct phishing tests within an organization. They'll send a fake phishing email to everyone in the company, and then send anyone who falls for the trap to an online cyber security seminar.
Educating employees about cyber security builds a culture of personal accountability within an organization.
Strengthen Your Password Security
A weak password is one of the easiest ways to let a hacker into your personal accounts. A trap that many people fall into is repeating passwords across multiple accounts.
Even if your password is strong, all it takes is a hacker accessing one account associated with that password to grant them access to all related accounts. Limit repeating passwords and refrain from writing them down anywhere when possible.
Although writing down passwords in an Excel spreadsheet or in the Notes app on your phone is convenient and keeps you from having to remember all your logins, this leaves the door open for someone with bad intentions to discover and take advantage of this information.
If you must write down passwords, consider a secure password-storing program. These programs store all your account logins in one secure location and then auto-fill the login forms when you visit an associated website.
If you ever want to view your stored passwords, simply log into the storage program, which is protected by multiple layers of security. When it comes to creating secure passwords, we have a few quick tips that you should keep in mind.
Refrain from including personal information in your passwords that can easily be found online. This includes everything from your birthday to your children's names to your alma mater.
While personal information helps make passwords more memorable, you should use specific information that only you would know. For instance, your password could include the name of your favorite vacation spot from your childhood or your favorite food you ate growing up.
Passphrases are another easy way to make a memorable password that's hard to crack. Passphrases are formed by taking 3-4 random words and stringing them together.
For instance, a passphrase could be "blue frog mountain pyrex". Although this password is easy to read and remember, according to the website How Secure Is My Password, this phrase would take a computer over 4 sextillion years to crack!
Hardware/Software Upgrades and Updates

Effectively securing your network requires multiple layers of hardware such as a firewall and software such as an antivirus.
Technology changes so rapidly that your old software and hardware may quickly become outdated after you buy them, especially if you don't stay current with updates. While software updates can seem tedious, many providers allow for automatic update scheduling, which takes the burden off of you.
When possible, automate software updates. Every time you forget to update your software, your network security lags further and further behind. Software updates help patch security gaps.
Along with updating your software whenever newer versions are released, consider periodically upgrading your hardware. While the cost for periodic upgrades can add up, if you're a business then you may be able to cut costs with a Managed Service Provider.
A Managed Service Provider (MSP) is a third-party company that manages your network security for you. Scheduled hardware upgrades can be built into your contract with them. Additionally, since they manage your cyber security for you, the burden of scheduling software updates is taken off of you.
MSP's can also help educate employees about cyber security best practices by implementing password policies, conducting phishing tests, and more.
While educating yourself about cyber threats is a great way to keep your network protected, don't stop there.
Email filters should be a piece of your cyber security infrastructure. However, keep in mind that the more layers of security you add means more barriers between your network and a hacker.
Use this article as a jumping off point to better secure your network today! Be sure to follow our blog for more cyber security tips and topics.
Posted by Erica Kastner

Erica Kastner is a lead Marketing Specialist at Standard Office Systems as well as a University of Georgia graduate. She aims to use her passion for problem-solving to help businesses understand how to better leverage their network infrastructure.

