PRINTER SECURITY | 4 MIN READ
With all the Internet-connected devices that now exist, it seems that almost any device can be targeted by a hacker. Can a printer be hacked? As a Managed Service Provider and printer dealer, our combined expertise in the.
cyber security best practices,
cyber security
Read More
CYBER SECURITY | 5.5 MIN READ
The finance, healthcare, and legal industries are frequently targeted for cyber attacks and are also subject to multiple data privacy regulations, which makes the task of effective and compliant cyber security difficult. As.
cyber security best practices,
cyber security solutions,
small business cyber security,
cyber security
Read More
CYBER SECURITY | 5 MIN READ
While email filtering has been around in one form or another for a while, it serves a more important role in your cyber security plan than you may think. Keep reading to learn what exactly email filtering is, how it works, and.
cyber security best practices,
cyber security
Read More
CYBER SECURITY | 4.5 MIN READ
Virtual Private Networks, known as VPN's, are a great asset to your business. By allowing your employees to access and share files on your network securely, you help mitigate the risk of data breaches. Keep reading to learn.
cyber security best practices,
cyber security solutions,
cybersecurity,
small business cyber security
Read More
CYBER SECURITY | 5 MIN READ
Expanding your company to multiple offices is an exciting development. When building new branches, you might not consider the necessary steps to set up your network to securely handle employees from multiple branches working.
cyber security best practices,
cyber security solutions,
cybersecurity,
small business cyber security
Read More
MANAGED IT SERVICES | 6 MIN READ
When shopping for managed IT services, you may come across the terms NOC and help desk. While they sound similar, nuanced differences between the two exist. Based on your business' needs, you may find that one is probably.
Managed IT Services,
Network Protection Atlanta,
Network Protection,
cyber security best practices,
cyber security solutions,
Managed IT Services Atlanta
Read More
CYBER SECURITY | 10.5 MIN READ
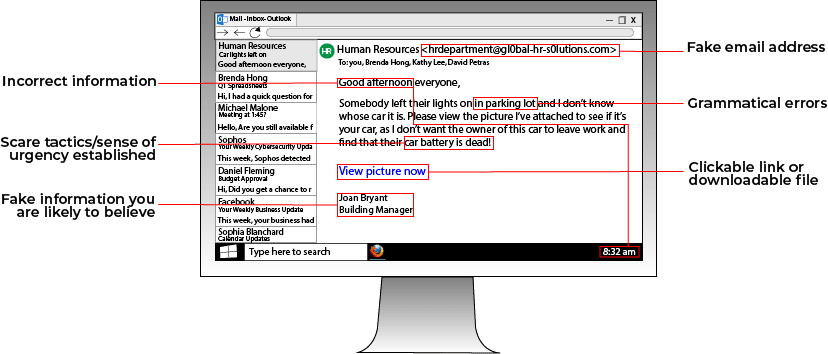
Major news outlets, from CNN to Forbes to the New York Times, have been reporting recently on the growing and shifting threat of ransomware. Just last week, the New York Times reported on the continued growth of ransomware.
cyber security best practices,
cybersecurity,
small business cyber security solutions,
ransomware and phishing
Read More
CYBER SECURITY | 4.5 MIN READ
The start of a new decade gives businesses a fresh start to strive towards achieving long-term goals. Businesses always think to set New Year's resolutions covering topics such as sales growth and business expansion..
cyber security best practices,
cybersecurity,
small business cyber security,
small business cyber security solutions
Read More
CYBER SECURITY | 5 MIN READ
Many cyber security terms are thrown around, which makes distinguishing one from another confusing. Malware has been making headlines for how prevalent it is. But what is it? Keep reading to learn a basic definition, the.
cyber security best practices,
cybercrime
Read More
CYBER SECURITY | 5.5 MIN READ
Employees are the heart and soul of a company. They keep the business running smoothly, managing business-critical tasks such as its financial stability. Though employees are responsible for keeping a company operating, they.
cyber security best practices,
cybersecurity,
small business cyber security
Read More
Much like pirates of yesteryear, pirates today steal what's most important and sell it on the Dark Web. In the 17th century, pirates sailed the seven seas in search of ships to board and treasures to plunder. The Golden Age of Piracy only lasted from.
cyber security best practices,
cyber security solutions,
cybersecurity,
small business cyber security
Read More